“Best-of-Breed”. I’ve always found that term interesting. It means selecting the best product there is in the market for your specific need. When you think about it, it is a great idea. Why not reach out and acquire the best widget for every single project? Different companies make different widgets and solutions for different purposes. Some are good, some are better, and some are the best. As you shop around the world of technology and acquire different solutions, you start to notice something…making these widgets and solutions work together requires a lot more time and attention than you realized. If you ever read the Choose Your Own Adventure book series, each choice could lead to success or headaches and disasters. Choosing solutions for the org should not be like that. Continue reading “Technological Synergy”
Reflections: 2024
It’s been a while! It has been a busy year or so since my last posting. I want to catch you up on things personal and professional. I also want to give you my thoughts on where folks will spend most of their time in the wide world of tech this upcoming year. Continue reading “Reflections: 2024”
My First Cisco Live
If you live in the world of technology, Cisco Live is one of the biggest events of the year. It’s an event where thousands come to learn and spend time with other like-minded individuals. There are exciting announcements, great speakers, and cool parties. It is the place to be. For years, I’ve always tried to attend, but it never worked out. The first year I received an actual approval to go to the conference was 2020, so the trip did not happen. Eventually I came over to Cisco. Even here though, it was not a guarantee I could attend the conference. Finally, this year I was selected with a few other colleagues to represent the team and attend with our customers. It was an outstanding experience and I want to tell you all about it! Continue reading “My First Cisco Live”
Why Cisco Meraki Makes Sense
What do many IT teams want? Simplicity. They want to see simplicity not only in the implementation of a solution, but in its operation and troubleshooting. However, often times we end up implementing complicated solutions or making them more complicated than necessary. Before you know it, only EngineerA knows how it works. If EngineerA leaves the org, everything falls apart. It should not be that way. It does not make business sense. What does make business sense is the way Cisco Meraki makes things simpler for enterprise networks around the world. Let’s take a look at three ways Cisco Meraki does this. Continue reading “Why Cisco Meraki Makes Sense”
From Ops to Sales
It’s been about nine months since I made the jump from an operational role to a sales role. I have been in operational roles my entire career, so it was a different direction moving into a Systems Architect role at Cisco. These months have flown by and its been great to see the other side. If you are thinking about making the move from ops to a sales role but are unsure of what to expect, keep on reading. I’ll be diving in to some of the myths I’ve heard. Continue reading “From Ops to Sales”
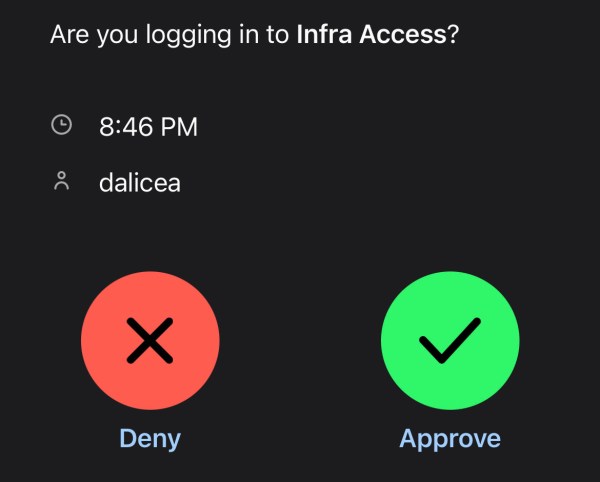
MFA All Things: Infrastructure
By now you should know that username and Password123 are not enough to protect access to your data. Even creating a complex password or a pass-phrase (which you should do) might not help you when your info gets dumped out on the internet from the latest data breach. Multi-factor Authentication (MFA) can help add another layer of verification to make sure you really are the person who is going to access a resource and not just someone who knows a username and password. In this entry, we will use Duo as our MFA solution with Cisco ISE configured for Device Management to verify who I am when I try to login to a network switch. Continue reading “MFA All Things: Infrastructure”
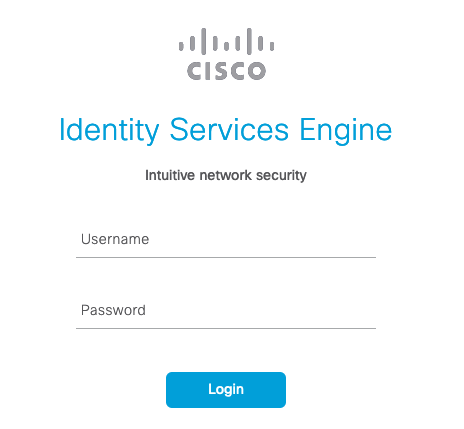
Device Management with Cisco ISE
Cisco’s Identity Services Engine (ISE) allows network and security teams to implement policy enforcement and weave in network access control in an automated fashion. ISE provides the visibility to allow intelligent decision making that gives administrators granular control. This granular control serves as a benefit when it comes to managing devices. What does Device Management look like with ISE? How do we utilize TACACS+ based AAA to give administrators granular control? This blog entry will dive into those details. Continue reading “Device Management with Cisco ISE”
The Career Change
We make choices everyday. Some of the choices are simple. Do I wear pajama pants or jeans today? Am I having breakfast? Do I want coffee? Whether it is a yes or no, those choices are not life changing. However, once in a while there are more complex choices to make. Do I want to move to a different company? Is it time for a career change? Those questions are not easily answered. They require thought. Big changes impact your life. They can impact your family’s lives. Wanting to grow and wanting more led me to ask those questions. The answers led me to a change from a life in operations into a sales role. Continue reading “The Career Change”