“Best-of-Breed”. I’ve always found that term interesting. It means selecting the best product there is in the market for your specific need. When you think about it, it is a great idea. Why not reach out and acquire the best widget for every single project? Different companies make different widgets and solutions for different purposes. Some are good, some are better, and some are the best. As you shop around the world of technology and acquire different solutions, you start to notice something…making these widgets and solutions work together requires a lot more time and attention than you realized. If you ever read the Choose Your Own Adventure book series, each choice could lead to success or headaches and disasters. Choosing solutions for the org should not be like that. Continue reading “Technological Synergy”
Why Cisco Meraki Makes Sense
What do many IT teams want? Simplicity. They want to see simplicity not only in the implementation of a solution, but in its operation and troubleshooting. However, often times we end up implementing complicated solutions or making them more complicated than necessary. Before you know it, only EngineerA knows how it works. If EngineerA leaves the org, everything falls apart. It should not be that way. It does not make business sense. What does make business sense is the way Cisco Meraki makes things simpler for enterprise networks around the world. Let’s take a look at three ways Cisco Meraki does this. Continue reading “Why Cisco Meraki Makes Sense”
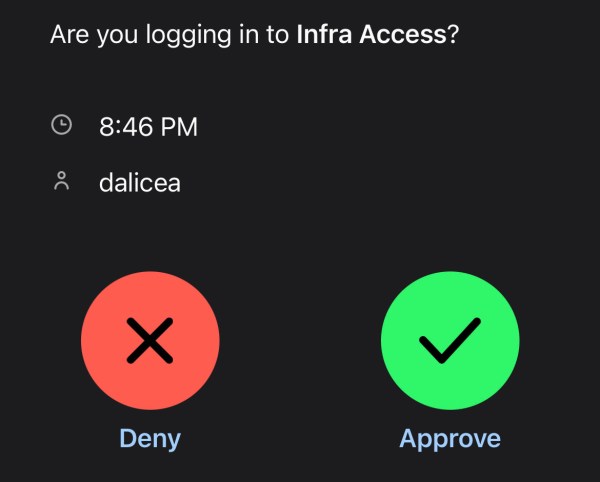
MFA All Things: Infrastructure
By now you should know that username and Password123 are not enough to protect access to your data. Even creating a complex password or a pass-phrase (which you should do) might not help you when your info gets dumped out on the internet from the latest data breach. Multi-factor Authentication (MFA) can help add another layer of verification to make sure you really are the person who is going to access a resource and not just someone who knows a username and password. In this entry, we will use Duo as our MFA solution with Cisco ISE configured for Device Management to verify who I am when I try to login to a network switch. Continue reading “MFA All Things: Infrastructure”
Firepower, ISE, and Duo: VPN Config
When it comes to a user’s Remote Access, Cisco’s AnyConnect has been a leader. It just works. That has been my experience as a user. That experience is also consistent for a user if their remote connection has a headend of an ASA or Firepower. However, one thing to note is that the backend administration and setup of Remote Access is different between the two. The ASA’s Remote Access setup has many bells and whistles that Firepower does not, but Firepower’s setup is pretty simple. We’re going to be setting up Remote Access using Firepower, but we are also going to leverage the Cisco Identity Services Engine for authorization policies as well as Cisco Duo for that extra layer of Multi-Factor Authentication protection. Continue reading “Firepower, ISE, and Duo: VPN Config”
Engineering Our Qualities
What is the most important thing you need to learn about in order to succeed in your IT career? Is it mastering a certain system? Is it programming like an expert? Is it creating the best disaster recovery plan? Maybe. Those can be individual accomplishments that can help open doors. However, once you have your foot in the door, how do you maintain a presence that can continue to elevate you in the workplace? It’s great to know everything, but if your attitude stinks your value drops. I put much more value on those humble techs and engineers who try their best, have good attitudes, and are there when their colleagues need them. It’s tough to show those qualities on paper, but they do get noticed by good leadership. I am going to bring up a few qualities that I believe are important to have for anyone that wants to shine in their role. Continue reading “Engineering Our Qualities”
Adventures in Troubleshooting: Chapter 1
To quote the late Bob Ross, “It’s hard to see things when you are too close. Take a step back and look.” When you are in the middle of those early morning troubleshooting sessions, it can be easy to panic. First, you are dealing with being woken up abruptly; everything is fuzzy. Then the person on the other end of the line might not be able to explain exactly what is happening. This combination usually leads to some fun times, sarcastically speaking. The best advice is to take that step back and look at the overall picture. No matter what your troubleshooting approach might be, the goal is to have one. The worst thing you can do is aimlessly wander around hoping to bump into the solution. In this entry I will dig into my mental ticket system of random issues I’ve ran into over the years, pull out three, and cover how those issues were resolved. Continue reading “Adventures in Troubleshooting: Chapter 1”
2021: Thinking Forward
Who doesn’t love to make plans and have goals? It’s January of 2021. Let’s not discuss what happened last year. Many of us accomplished different things and many of us did not. No matter what happened last year, I’d like to look forward to making plans for this year. However, making plans is not enough. Executing is what needs to happen. Sometimes our execution is derailed by many outside factors throughout the year. This will happen. I believe it is best not to thrust all of our worries on the things we cannot control. Let’s focus our energy on the what is within our reach. As a network engineer, there are a few goals I want to briefly write about. I am hoping writing it will help keep me accountable. Continue reading “2021: Thinking Forward”
2020 Cisco IT Blog Awards
I have been nominated as a finalist in the 2020 Cisco IT Blog Awards! I feel blessed to have something I started last year be selected. My main goal in my blog is to motivate others in their IT career. We are all in this together. I have been selected as a finalist for the Most Inspirational category. One thing is for certain, I love to write and I love to motivate.
My one ask as we close this year out is that you take a moment and vote. Look through all the blogs and follow all of the good talent out there in each category. The winners will be announced early next year.
You can vote and check out the entries here: https://www.ciscofeedback.vovici.com/se/705E3ECD2A8D7180