“Best-of-Breed”. I’ve always found that term interesting. It means selecting the best product there is in the market for your specific need. When you think about it, it is a great idea. Why not reach out and acquire the best widget for every single project? Different companies make different widgets and solutions for different purposes. Some are good, some are better, and some are the best. As you shop around the world of technology and acquire different solutions, you start to notice something…making these widgets and solutions work together requires a lot more time and attention than you realized. If you ever read the Choose Your Own Adventure book series, each choice could lead to success or headaches and disasters. Choosing solutions for the org should not be like that. Continue reading “Technological Synergy”
Why Cisco Meraki Makes Sense
What do many IT teams want? Simplicity. They want to see simplicity not only in the implementation of a solution, but in its operation and troubleshooting. However, often times we end up implementing complicated solutions or making them more complicated than necessary. Before you know it, only EngineerA knows how it works. If EngineerA leaves the org, everything falls apart. It should not be that way. It does not make business sense. What does make business sense is the way Cisco Meraki makes things simpler for enterprise networks around the world. Let’s take a look at three ways Cisco Meraki does this. Continue reading “Why Cisco Meraki Makes Sense”
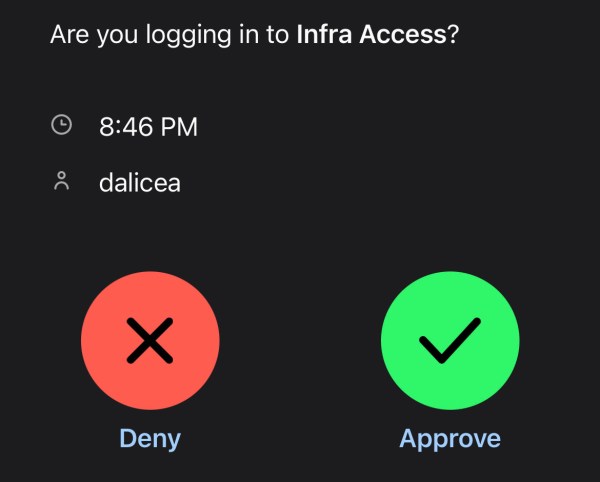
MFA All Things: Infrastructure
By now you should know that username and Password123 are not enough to protect access to your data. Even creating a complex password or a pass-phrase (which you should do) might not help you when your info gets dumped out on the internet from the latest data breach. Multi-factor Authentication (MFA) can help add another layer of verification to make sure you really are the person who is going to access a resource and not just someone who knows a username and password. In this entry, we will use Duo as our MFA solution with Cisco ISE configured for Device Management to verify who I am when I try to login to a network switch. Continue reading “MFA All Things: Infrastructure”
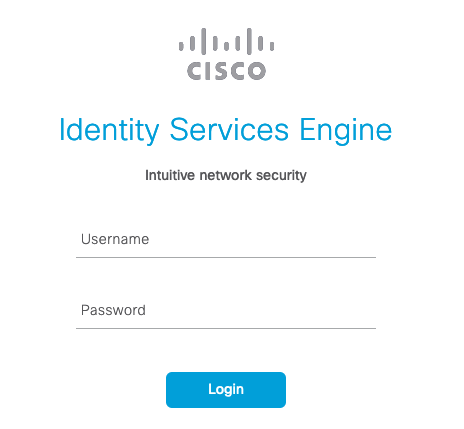
Device Management with Cisco ISE
Cisco’s Identity Services Engine (ISE) allows network and security teams to implement policy enforcement and weave in network access control in an automated fashion. ISE provides the visibility to allow intelligent decision making that gives administrators granular control. This granular control serves as a benefit when it comes to managing devices. What does Device Management look like with ISE? How do we utilize TACACS+ based AAA to give administrators granular control? This blog entry will dive into those details. Continue reading “Device Management with Cisco ISE”
The Occasion for Segmentation
Today’s networks have security and visibility requirements that can warrant complicated designs. A proper routing design takes time. Implementing security takes some thought. Having a properly segmented network goes beyond tossing a bunch of VLANs on a switch. One of the goals in a segmentation design is to engage the business and find out the who, what, where and why of communication in the network. If you know those business purposes, you can design around it. You can implement routing and firewall rules to control who or what has access to certain assets. In this entry to the blog, I have implemented a basic segmented network using EVE-NG. Let’s take a tour! Continue reading “The Occasion for Segmentation”
DNS Security With Palo Alto
I blame DNS! Oh wait, that’s not what I am writing about. Domain Name Service (DNS) is a foundational piece to communication. Unless you know every IP address for every website you want to visit, you are going to need DNS. Users and services all over the world rely on DNS to seamlessly communicate. What a great opportunity for attackers to lead users to malicious destinations. DNS Security provides us a way to stop malicious requests from users’ devices from ever reaching those destinations. There multiple solutions out there to secure the DNS-layer. The focus of this entry is to explore Palo Alto’s solution to DNS Security. Continue reading “DNS Security With Palo Alto”
Image Swap: ASA to FTD
Firewalls are a necessary component in any network environment, especially in an enterprise. Take a look at your front door, would you remove it permanently? Firewalls have evolved over the years from simple gatekeepers to complex security solutions that integrate with the rest of the network. Imagine if you could program your front door to only allow people in who wore green shirts. Once inside they would only be able to walk into the living room…on a Tuesday. My own firewall journey started years back on Juniper SSG350s then onto ASA and Palo Alto. I am currently looking into Cisco’s Firepower Threat Defense (FTD). As a fan of most things Cisco (ASA CX anyone?), FTD adds visibility to the rest of the ecosystem that might include AMP, ISE and Stealthwatch. With an ASA 5512-X in hand, my mission is to replace its ASA image with FTD. Continue reading “Image Swap: ASA to FTD”
Do it Live: Cisco Umbrella
Can you give me a list of all the destinations employees at your company are browsing to on the internet in the office and out? Would you know if all of those sites are safe? Are they clicking on those “Free Tablet Just For You!!!!!!” email links? The internet can be a dangerous place. DNS helps users easily reach destinations. Who is going to remember the IP addresses to hundreds of sites? However, DNS can lead users to malicious destinations as well. You might have a need to protect users or enforce company policies at the DNS level.
This post will be a review of Cisco Umbrella. We’ve been using it in production. This will by no means serve as deployment instructions. Please refer to Cisco Umbrella’s documentation for those. These are just my thoughts on how the process went. Continue reading “Do it Live: Cisco Umbrella”